The threat of data breaches is rising
Cyberthreats are quickly becoming more costly and complex. Your customers know this - you need a powerful solution to keep their personal information safe. Carat provides a multi-layered solution to protect sensitive card data at every stage of the payment process.
of consumers won't buy from a company they have security concerns about1
Data loss by the numbers
4.45
Maverage cost of a data breach2
40
%of lost business is associated with data breaches3
52
%of all data breaches in 2023 have involved a form of customer PII4
Comprehensive data protection
Confident customers are more likely to repeat business. Optimize customer payment data with a multi-layered data protection strategy to protect data in transit and at rest across omnichannel environments.

Encryption
Uninterrupted protection as payment data moves across channels, networks, and partner environments.

Tokenization
Replace sensitive payment data with omnichannel tokens which can be used across your environment.
Leverage tokens across all channels
Better engage with your customers without storing sensitive data. Every customer has a unique token that follows them across your diverse sales channels, allowing you to better understand their behavior and drive more effective marketing and loyalty programs.

1
Wearable smart watch

2
GPS navigation
3
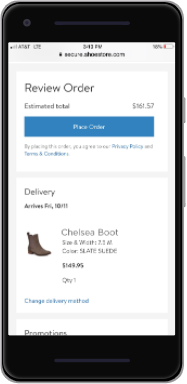
Checkout page on smartphone
4
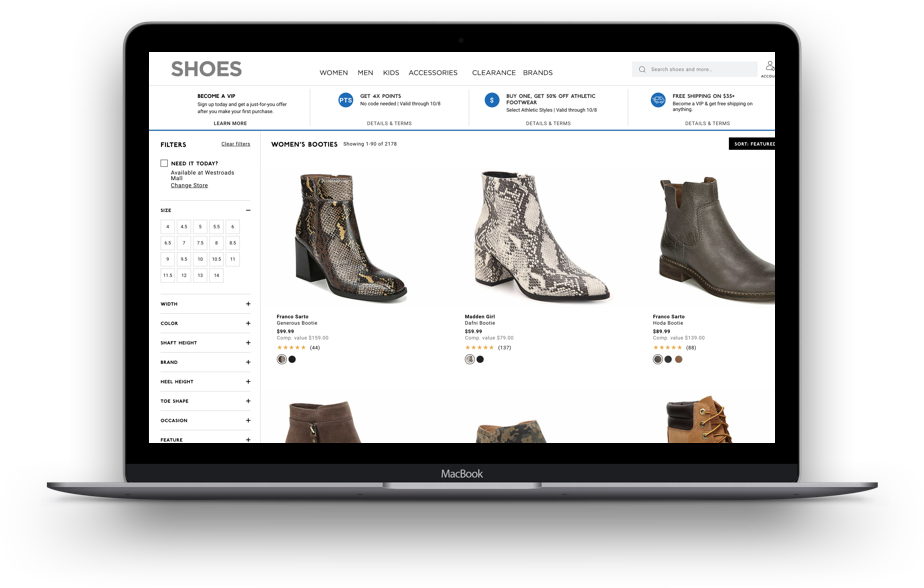
eCommerce website on laptop
Reduce PCI scope with a PCI validated P2PE solution
Reduce your compliance scope up to 90% so you can focus on growing your business.3 Our PCI Validated Point-to-Point Encryption (P2PE) solution delivers better security and significantly increases PCI compliance.

Significant Scope Reduction
Leverage our multi layered security solution to fulfill most of your PCI requirements, so you can focus on your customers.
Requirement Responsibilities
P2PE reduces your compliance responsibilities to only three requirements. This includes protecting stored paper cardholder data, restricting physical access to cardholder data, and maintaining an information security policy.
Ideas and inspiration
Tell us your vision and we'll bring the solution
We will work with you to understand your business needs and show you how to best leverage our solutions to make your vision a reality.
Sources: 1. McKinsey, 2. IBM Security, 3. CSO, 4. IBM Security




